SCI, SSCI ve AHCI İndekslerine Giren Dergilerde Yayınlanan Makaleler
Server assisted signatures revisited
Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics)
, cilt.2964, ss.143-156, 2004 (SCI-Expanded)


Improving the Security and Flexibility of One-Time Passwords by Signature Chains
Turkish Journal of Electrical Engineering and Computer Sciences
, cilt.11, sa.3, ss.223-236, 2003 (SCI-Expanded)


How to construct optimal one-time signatures
COMPUTER NETWORKS-THE INTERNATIONAL JOURNAL OF COMPUTER AND TELECOMMUNICATIONS NETWORKING
, cilt.43, sa.3, ss.339-349, 2003 (SCI-Expanded)









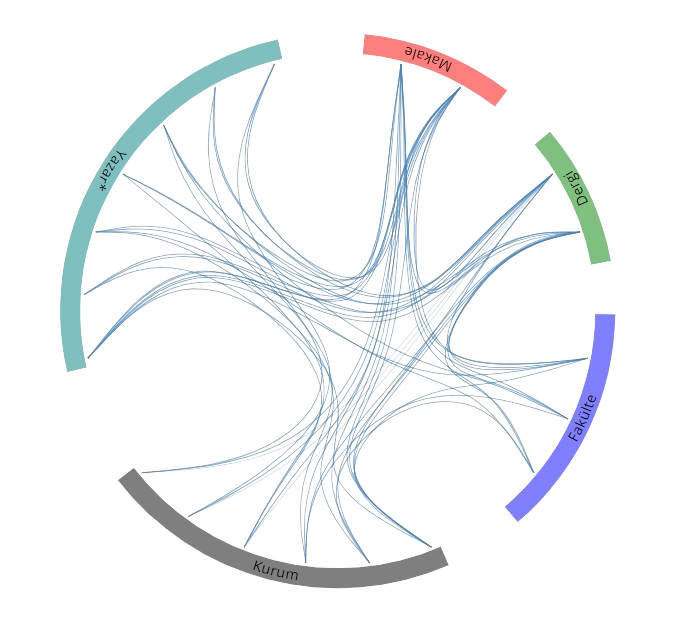 Yayın Ağı
Yayın Ağı